
4.9 (78) · $ 306.00 · In stock
Description

Malware Posing as Russia DDoS Tool Bites Pro-Ukraine Hackers - vulnerability database
Research at the DAO - PhilaDAO Data Dashboard

Consulting and Technical Advisory

PDF) Strategy Implementation and Public Service Performance
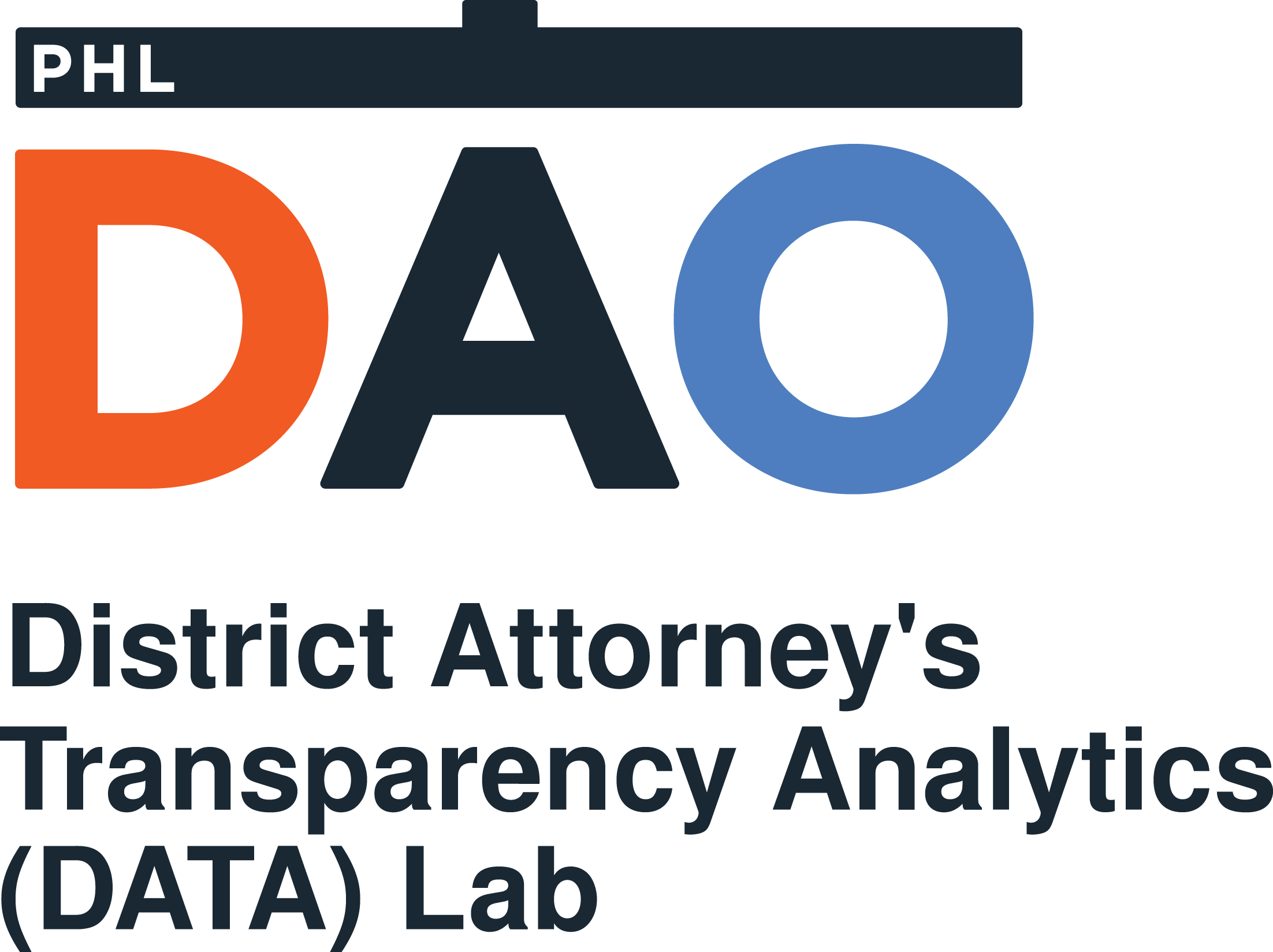
Assess Your Risk From Ransomware Attacks, Powered by Qualys - vulnerability database
Frame Your Question Implementation Science at UW
China suspends deal with Alibaba for not sharing Log4j 0-day - vulnerability database

Cyberattackers Leverage DocuSign to Steal Microsoft Outlook - vulnerability database
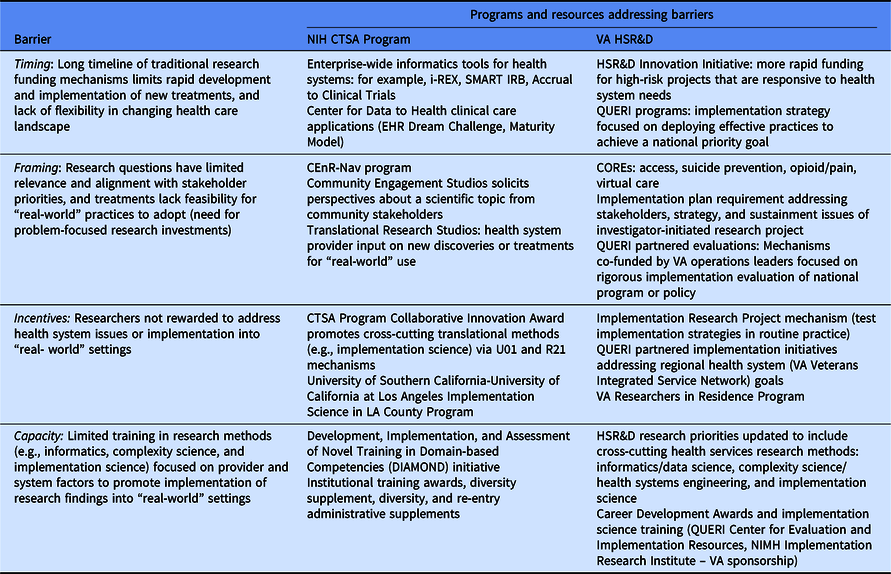
Accelerating implementation of research in Learning Health Systems: Lessons learned from VA Health Services Research and NCATS Clinical Science Translation Award programs, Journal of Clinical and Translational Science
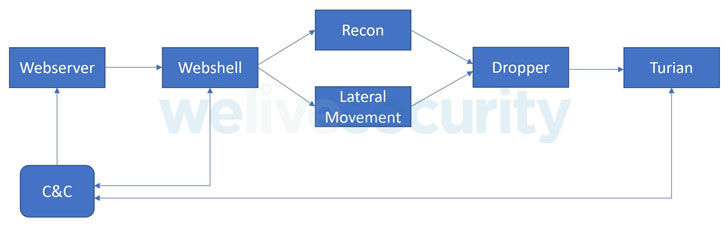
New Cyber Espionage Group Targeting Ministries of Foreign Af - vulnerability database

PDF) Community-based implementation strategy use and satisfaction: A mixed- methods approach to using the ERIC compilation for organizations serving children on the autism spectrum

Research at the DAO - PhilaDAO Data Dashboard
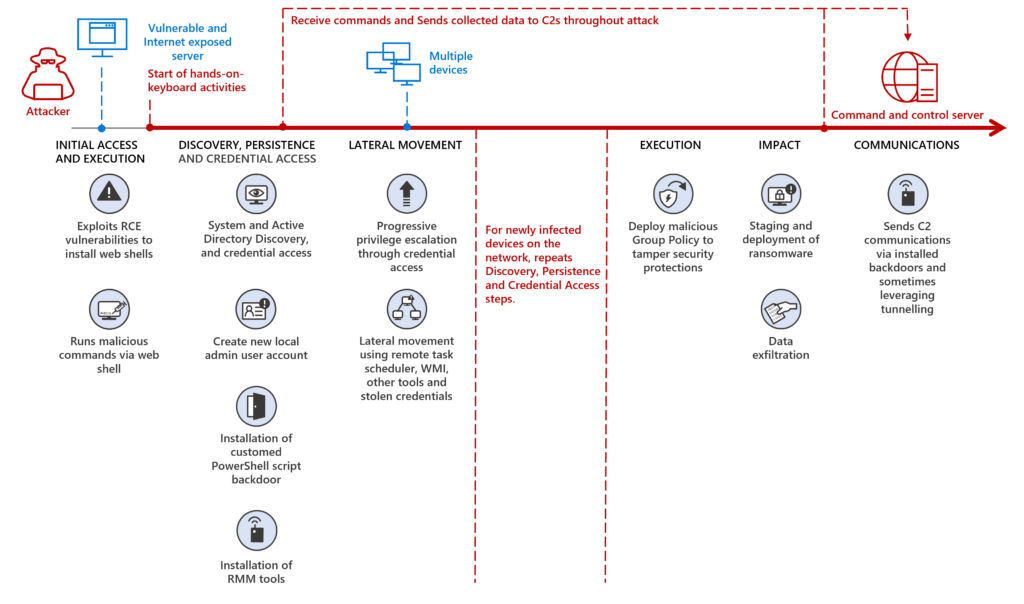
MERCURY and DEV-1084: Destructive attack on hybrid environme - vulnerability database
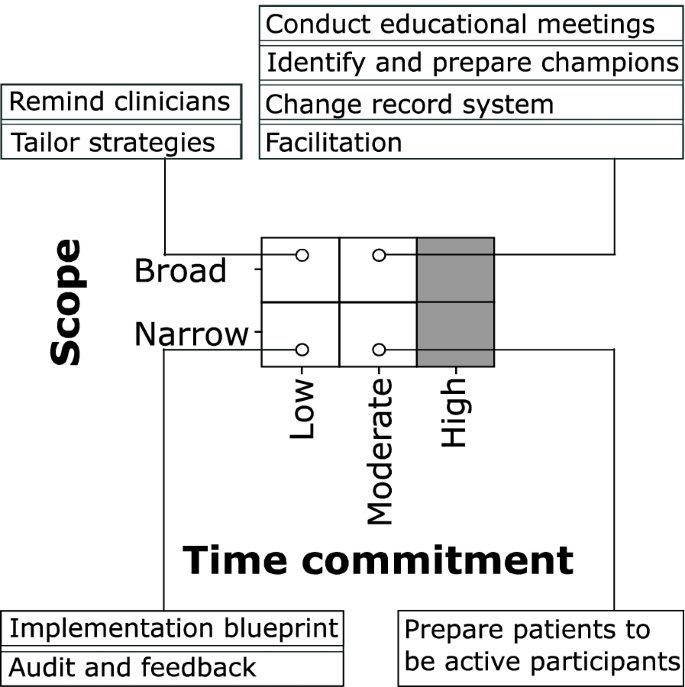
Data-driven approach to implementation mapping for the selection of implementation strategies: a case example for risk-aligned bladder cancer surveillance, Implementation Science
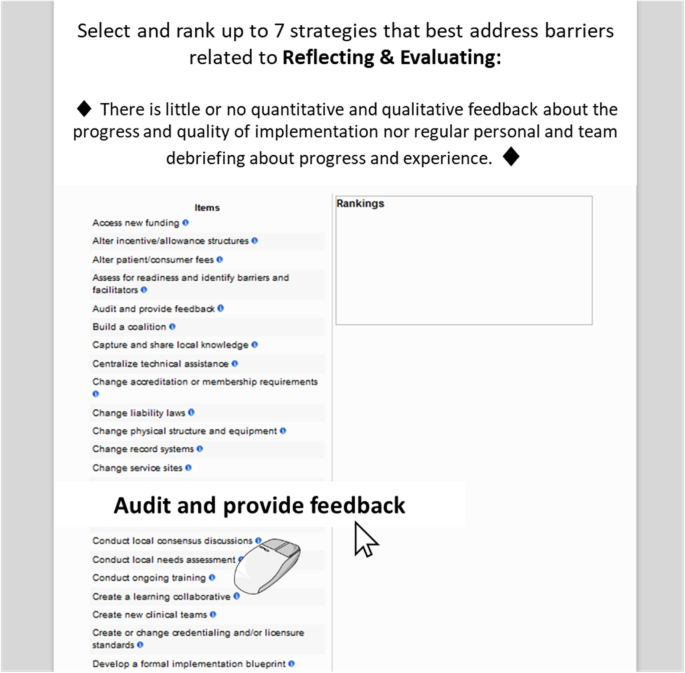
Choosing implementation strategies to address contextual barriers: diversity in recommendations and future directions, Implementation Science